Negotiating With Ransomware Hackers
Brought to you by Booz Allen Hamilton
One of the most serious cyber events that any company can experience is a ransomware attack where the hackers either encrypt or steal critical data, and demand an immediate multimillion-dollar ransom payment.
Speed is vital when dealing with ransomware attacks. The first step is to implement the company’s incident response plan to identify the extent of the attack and contain it before it spreads further. That is, if the company has an incident response plan. Unfortunately, many companies today still don’t have a plan, which causes unnecessary delays and confusion.
A strong response plan spells out all the things that need to happen when an attack has occurred, including which outside experts to immediately engage. Having these arrangements worked out in advance allows the company to move quickly. When a hacker breaches an organization, they send a note with directions on how to contact them – and they expect a quick response. In one recent engagement, a client without an incident response plan in place waited seven days before contacting us. The hacker had a policy of doubling its demand if the target company did not respond to its note within three days, so the demand skyrocketed to $24 million.
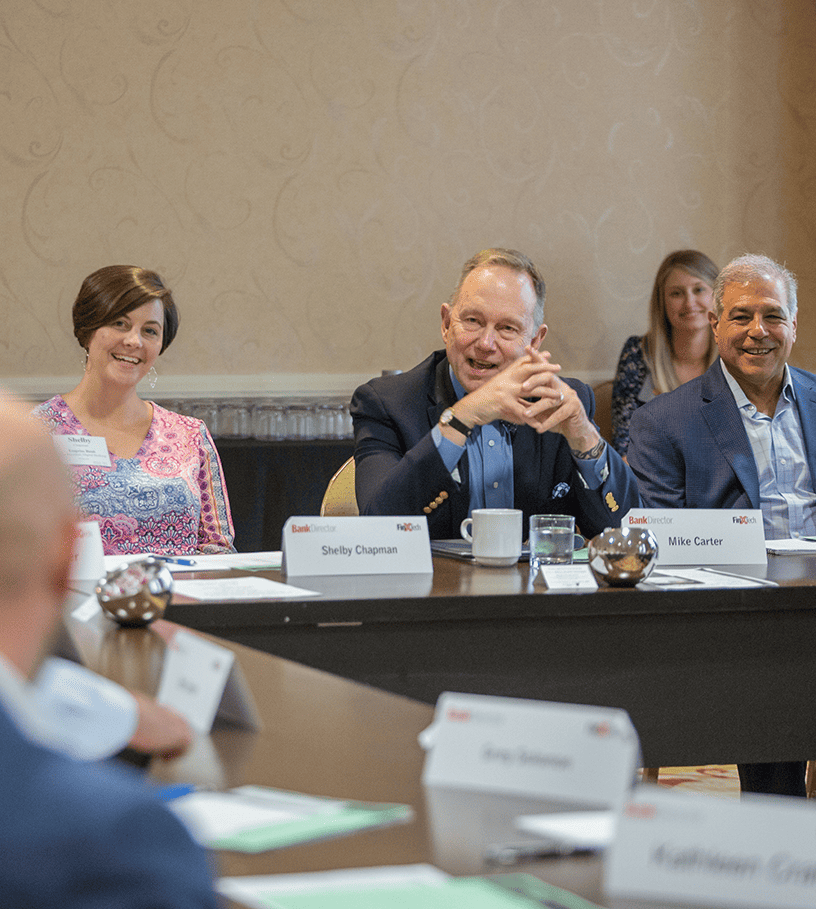
Communications, Negotiations
People treat robbery victims with concern and comfort. Despite the similarities, ransomware victims are often shunned by partners and vendors who attempt to firewall themselves off from potential damage. This makes communication a critical component for everyone with whom the firm does business. We help leadership identify the partners they need to closely engage for business continuity.
One of the first questions that ransomware victims ask is whether to negotiate with the hackers. The attackers try to stir up a crisis to goad their victims into quickly paying, often targeting the company’s senior executives personally to up the ante. Communicating with the hackers can help de-escalate the situation into something more like a business negotiation.
Having seen a wide spectrum of cases, we are able to identify and prioritize response gaps. For example, is the client engaged with law enforcement? How should legal and insurance partners be brought in?
Technically, we quickly help the client identify what critical systems and data might have been affected to understand the significance of the event. Understanding the extent of the intrusion allows leadership to clearly articulate the impact of the attack with a plan forward, which is often critical to faster recovery, as everyone understands how well the problem is addressed.
In situations where clients have decide not to pay a ransom, we have been successful in helping them rebuild systems and get back in operation without decryption.
When a company pays a ransom, often what it is paying for is the hacker-owned decryption key that will “unlock” the data. A skilled negotiator should be able to secure a reduced price for the key, which is more expedient than rebuilding the systems from scratch.
Many companies used to believe they needed to make every effort to reclaim their data, even if it appeared to us to have little monetary value or would not create a competitive disadvantage for the company if it were released. This is changing, as companies are beginning to understand the long-term effects of paying ransom. It does not make the victim company immune from future attacks; it provides the attackers with capital to build more sophisticated tools and hire more affiliates to initiate more attacks. Ransoms also make the attackers increasingly difficult to negotiate with going forward.
Paying A Ransom?
Remember: The motivation of ransomware hackers is money. They want to get paid quickly. A company’s data has no value to them, other than the leverage it affords them to extort a ransom.
We never recommend that clients pay or not pay a ransom. We provide our clients with the best assessment possible of their current situation and potential outcomes, but ultimately it is their decision. Further, we recommend the client take significant steps to both ensure the full extent of the attack has been addressed, and that systems and processes are updated to prevent future attacks.
It’s worth noting that ransomware hackers would soon be out of business if the majority of companies had the kind of robust defenses in place that can protect their data from an attack, as well as a comprehensive incident response plan. The most tragic thing about successful ransomware attacks is that they are preventable.