From how-to articles, director training videos, key interviews with industry leaders and more, Bank Services provides bank executives and directors with the tools to help grow their financial institutions.rnrnTo sign up for exclusive access to this online bank board resource, please contact Bank Services at 615-777-8461 or [email protected].

The New Regulatory Expectation for Cybersecurity Assessment: What Every Board Must Know & Should Do
 Earlier on June 11, 2015, while serving as a keynote speaker on cybersecurity at Bank Director’s Bank Audit and Risk Committees conference in Chicago, I predicted that the regulatory agencies would publish a new cybersecurity assessment methodology by the end of the month.
Earlier on June 11, 2015, while serving as a keynote speaker on cybersecurity at Bank Director’s Bank Audit and Risk Committees conference in Chicago, I predicted that the regulatory agencies would publish a new cybersecurity assessment methodology by the end of the month.
That prediction came true and the Federal Financial Institutions Examination Council (FFIEC) on June 30, 2015, released the cybersecurity assessment tool. Examiners will start to use the cybersecurity assessment later in the year and there is a regulatory expectation that every single financial institution, regardless of charter type, asset size or complexity, complete a self-assessment and keep it updated.
What Is the Cybersecurity Assessment?
The main purpose is to provide a financial institution with a self-assessment method that is measurable and repeatable to identify risk exposures and cybersecurity preparedness.
The first step is to identify the institution’s inherent risk level (least, minimal, moderate, significant or most) based on five categories of risk factors:
- Technologies and connection types
- Delivery channels
- Online/mobile products and technology services
- Organizational characteristics
- External threats
The next step is to identify the cybersecurity maturity level (baseline, evolving, intermediate, advanced or innovative) for each of five domains:
- Cyber risk management and oversight
- Threat intelligence and collaboration
- Cybersecurity controls
- External dependency management
- Cyber incident management and resilience
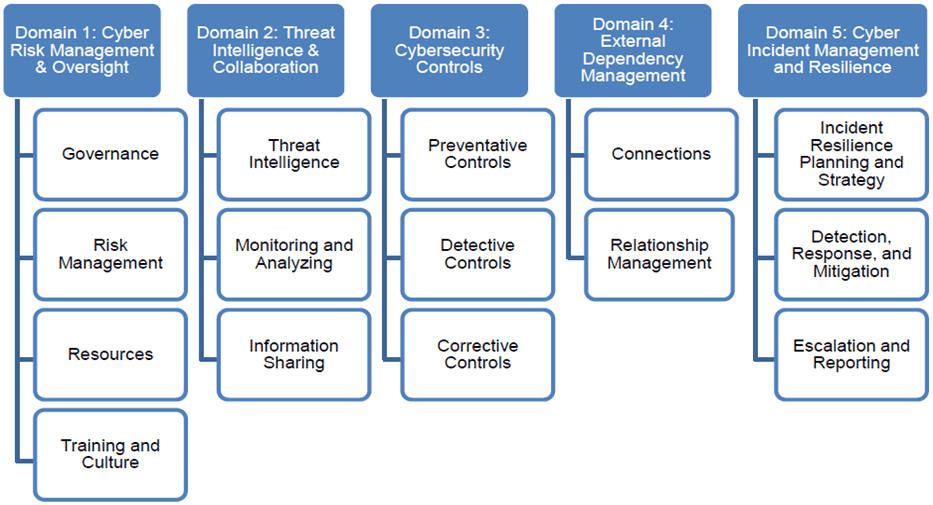 Source: FFIEC
Source: FFIEC
The next step is to identify the gaps and the target maturity level necessary for each of the five domains. The chart below depicts the risk/maturity relationship matrix and the “cybersecurity zone” in blue that each financial institution needs to attain and sustain in each domain:
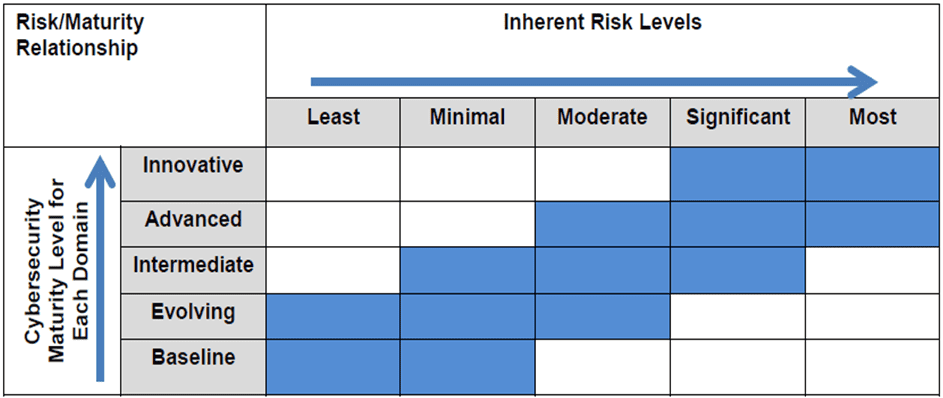 Source: FFIEC
Source: FFIEC
For example, if a financial institution with a moderate inherent risk level determines that its domain 3 or cybersecurity controls maturity level is baseline, then it will need to attain a target maturity level of evolving, intermediate or advanced (i.e. it will need to get to the “cybersecurity zone”) and sustain it. Staying at a baseline maturity level for the domain will be unacceptable given the moderate inherent risk level. In some cases, the institution may identify a maturity level below baseline, which will require immediate action.
The regulatory expectation is that once the initial cybersecurity assessment is completed, there will be an action plan identified to attain target maturity levels and to sustain it. Also the cybersecurity assessment will be updated and revaluated periodically as threats, vulnerabilities and operational environments change (e.g. launch of new products or services, new connections, etc.)
What Should the Board Do?
Examiners will be using the cybersecurity assessment to evaluate a financial institution’s risk level and cybersecurity preparedness and scoping examinations. Failing to complete the cybersecurity assessment and sustaining it may be deemed an unsafe and unsound practice and examiners will closely evaluate the board’s role and ultimately hold it accountable. Failing to complete an assessment may lead to unmitigated risks, a cyber disaster and a conclusion that the board failed to exercise its risk oversight and fiduciary duty.
Ultimately, the board is responsible for ensuring the organization completes the cybersecurity assessment and maintains a repeatable process to update it periodically. The cybersecurity assessment provides critical forward looking intelligence that the board should use to guide the organization to attain optimal cyber risk management performance, mitigate risks to a tolerable level and maximize shareholder value. The stakes are very high. Cybersecurity must remain top of mind and the board must lead.
Here are seven critical steps the board should take:
- Assign a target date for the completion of the cybersecurity assessment and reporting of results to the board, well in advance of the next examination. Provide necessary support to complete it properly and in a timely manner.
- Obtain independent review of cybersecurity assessment to validate results. Make sure there is proper support for inherent risk level and maturity level determinations. Pay extra attention to validation of baseline levels, because in reality, the bank may be below baseline.
- Review, approve and support action plan for addressing risk management and control weaknesses and attaining and sustaining target maturity levels.
- Make sure any levels below baseline are immediately addressed.
- Require that a repeatable and sustainable process be implemented so that the cybersecurity assessment is revaluated and updated periodically (based on board approved triggers) and results are reviewed with the board.
- Assign implementation of regular risk dashboard reporting to the board with leading, not lagging, key risk indicators mapped to the cybersecurity assessment.
- Require a cybersecurity assessment be completed as part of due diligence in a merger or acquisition and reviewed with the board.
You have accessed a resource that is only available to our Bank Services members.
Read The Article
Please enter your username and password bellow. If you have established a password please click ‘forgot your password’
You have accessed a resource that is only available to our Bank Services members.
From how-to articles, director training videos, key interviews with industry leaders and more, Bank Services provides bank executives and directors with the tools to help grow their financial institutions.rnrnTo sign up for exclusive access to this online bank board resource, please contact Bank Services at 615-777-8461 or [email protected].
Read The Article
Please enter your username and password bellow. If you have established a password please click ‘forgot your password’